Author: khirawdhi
-

When Threat Modeling Goes Wrong: Forcing Security Without Understanding the Trade-Off
Threat modeling is one of the most powerful tools in security architecture. When done correctly, it brings clarity. It reveals assumptions. It exposes blind spots. It helps engineering teams design systems that are resilient without becoming unnecessarily rigid. But when done poorly, threat modeling becomes something else entirely. It becomes control inflation. It becomes fear-driven…
-
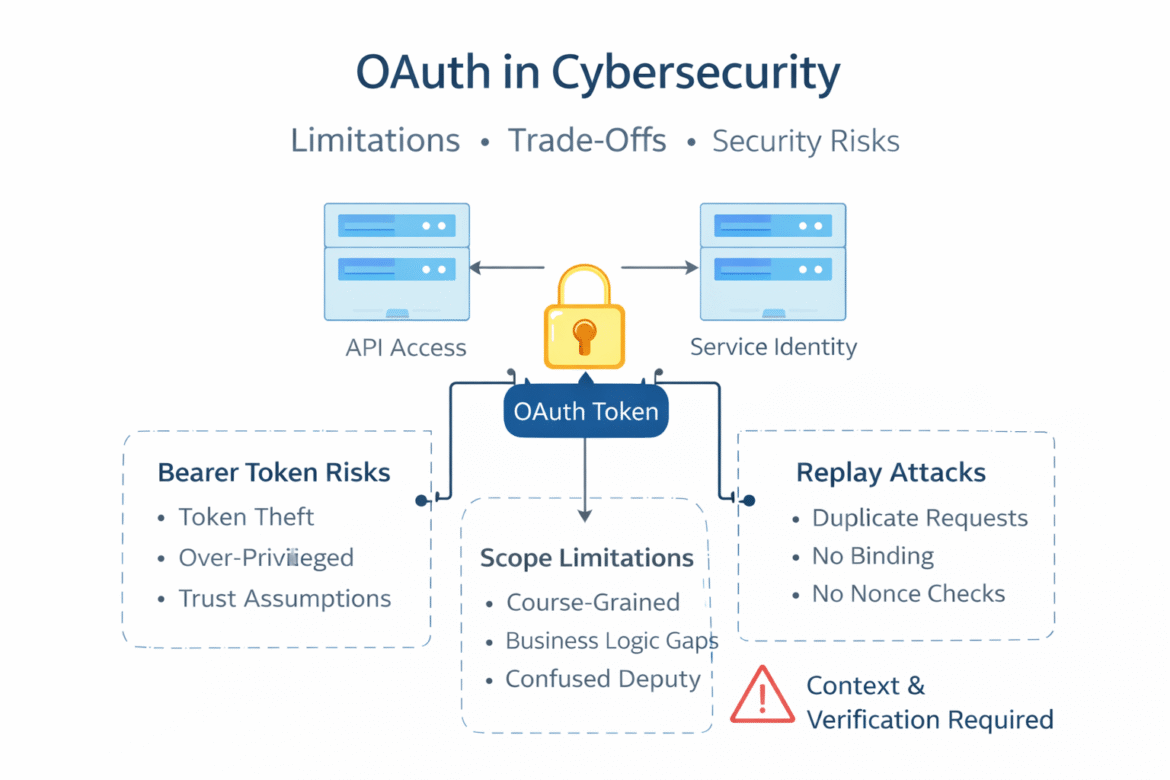
Is OAuth Enough? Security Limitations in Modern Systems
OAuth has become the backbone of modern authentication and authorization systems. It powers API access, mobile applications, SaaS integrations, service-to-service communication, and identity federation across organizations. It is often treated as a solved problem. It is not. OAuth is a powerful delegation framework, but it is frequently misunderstood, misapplied, or over-trusted. Its flexibility is both…
-
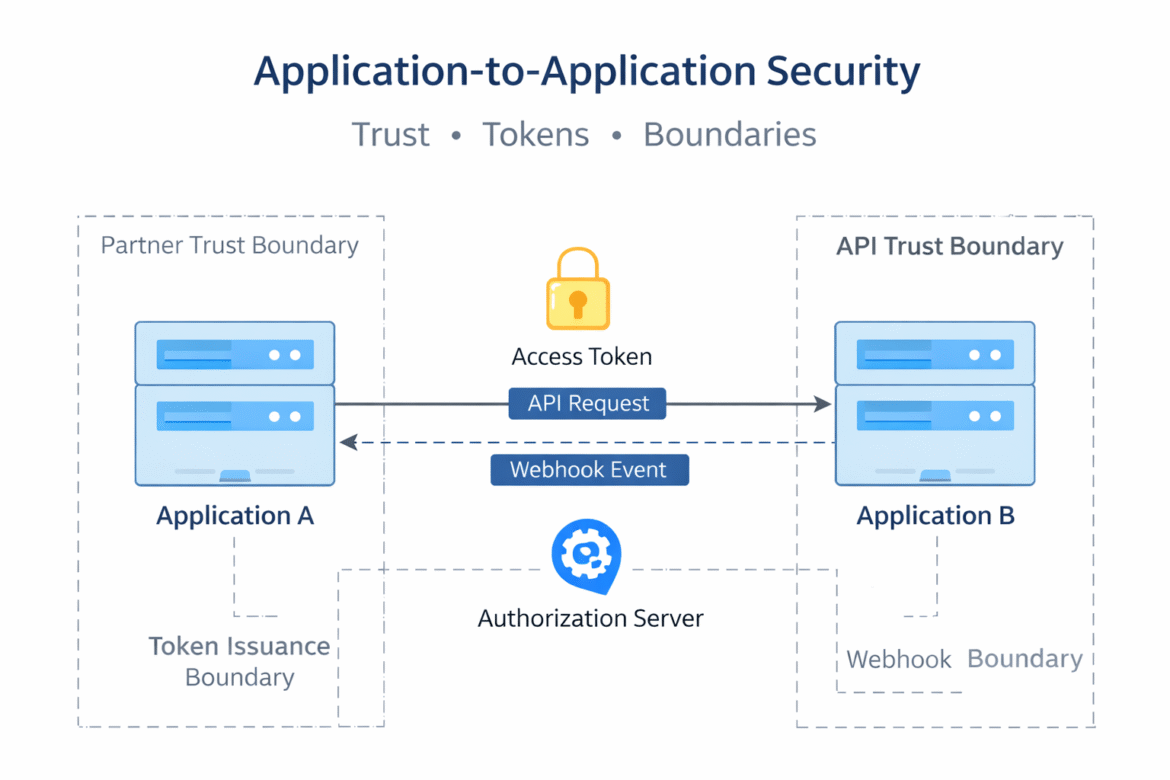
A2A Security Explained: Common Risks in Service-to-Service Integrations
Modern systems are no longer isolated applications. They are networks of services, partners, and platforms exchanging data and triggering actions across organizational boundaries. Application-to-Application (A2A) communication has become the backbone of SaaS ecosystems, internal microservices, and B2B integrations. Despite its importance, A2A security is often underestimated. Many teams assume that once authentication is in place,…
-

Threat Modeling as Architecture: How a Zero-to-Hero Cloud Playbook Scales
Most threat modeling guides start with STRIDE tables, tools, or workshops. In practice, that is often where things already go wrong. Threat modeling is not a checklist, a diagram, or a one-time security exercise. It is an architectural way of thinking about trust, identity, and failure especially in cloud-native systems. The real challenge is not…
-

The Silent Whistleblower: Cybersecurity Ethics in an Age of Hidden Truth
In modern cybersecurity, the most important whistleblower is rarely a person. It is a log line no one reviewed. A spike in outbound traffic normalized as “noise.” An IAM permission that technically worked but should never have existed. The digital age did not eliminate whistleblowers. It turned them silent. Today, truth leaks not through documents…