Category: Cloud Security
-

Threat Modeling as Architecture: How a Zero-to-Hero Cloud Playbook Scales
Most threat modeling guides start with STRIDE tables, tools, or workshops. In practice, that is often where things already go wrong. Threat modeling is not a checklist, a diagram, or a one-time security exercise. It is an architectural way of thinking about trust, identity, and failure especially in cloud-native systems. The real challenge is not…
-

From DevSecOps to MLSecOps: Securing the AI Development Lifecycle
In recent years, organisations have matured their software-development practices through models like DevSecOps integrating security (“Sec”) into the development (Dev) + operations (Ops) lifecycle. Now, as artificial intelligence (AI) and machine-learning (ML) systems become core to business operations, a new discipline is emerging: MLSecOps (Machine Learning Security Operations). MLSecOps takes the DevSecOps ethos but extends…
-
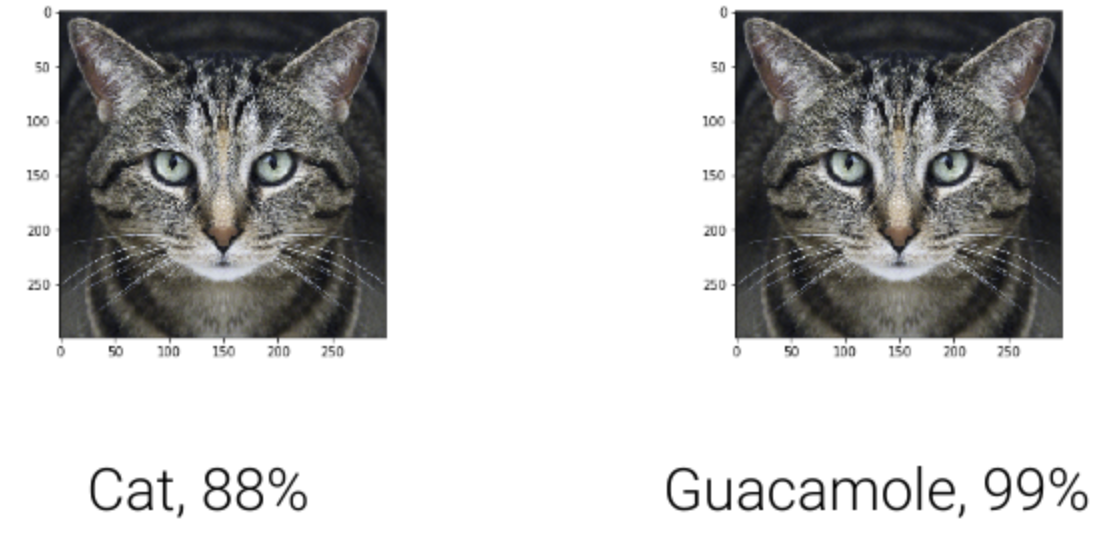
Adversarial AI in the Wild: Real-World Attack Scenarios and Defenses
AI is no longer just predicting clicks and classifying cats, it’s browsing the web, writing code, answering customer tickets, summarizing contracts, moving money, and controlling workflows through tools and APIs. That power makes AI systems an attractive, new attack surface often glued together with natural-language “guardrails” that can be talked around. This guide distills the…
-

Shadow AI: The Hidden Risk Lurking Inside Organizations
Artificial Intelligence (AI) has become the driving force behind innovation in enterprises optimizing operations, enabling predictive analytics, and enhancing decision-making. But with AI’s rapid adoption comes a dangerous byproduct: Shadow AI. Just as “shadow IT” once described unsanctioned apps and tools used without IT’s approval, Shadow AI refers to AI systems, models, and tools deployed…
-

ML Supply Chain Security: Protecting the Pipeline of Machine Learning
Machine Learning (ML) is the backbone of modern digital transformation, powering fraud detection, medical diagnostics, recommendation engines, and more. But with great adoption comes great risk. ML systems are not isolated models; they rely on a complex supply chain of data, frameworks, libraries, pre-trained models, APIs, and deployment pipelines. Each of these dependencies introduces security…