Category: Cloud Security
-

Rethinking Container Security: From Fragmented Practices to a Simple, Usable Flow
Containerization has transformed how we build and deploy software. With tools like Docker and Kubernetes, developers can move faster than ever before. At the same time, security practices around containers have grown rapidly, image scanning, runtime controls, and Kubernetes policies are now widely discussed and adopted. And yet, for many teams, container security still feels……
-
AI Can Fix Code, But Not Security: The Hidden Gap in Cybersecurity
AI is powerful at code-level fixes, but real-world security issues are rarely just code problems they are system, context, and environment problems. The Myth: “AI Will Fix Security Bugs Automatically” There’s a growing assumption: “If AI can generate code, it can fix vulnerabilities too.” This works in controlled environments: But real-world security engineering looks very…
-
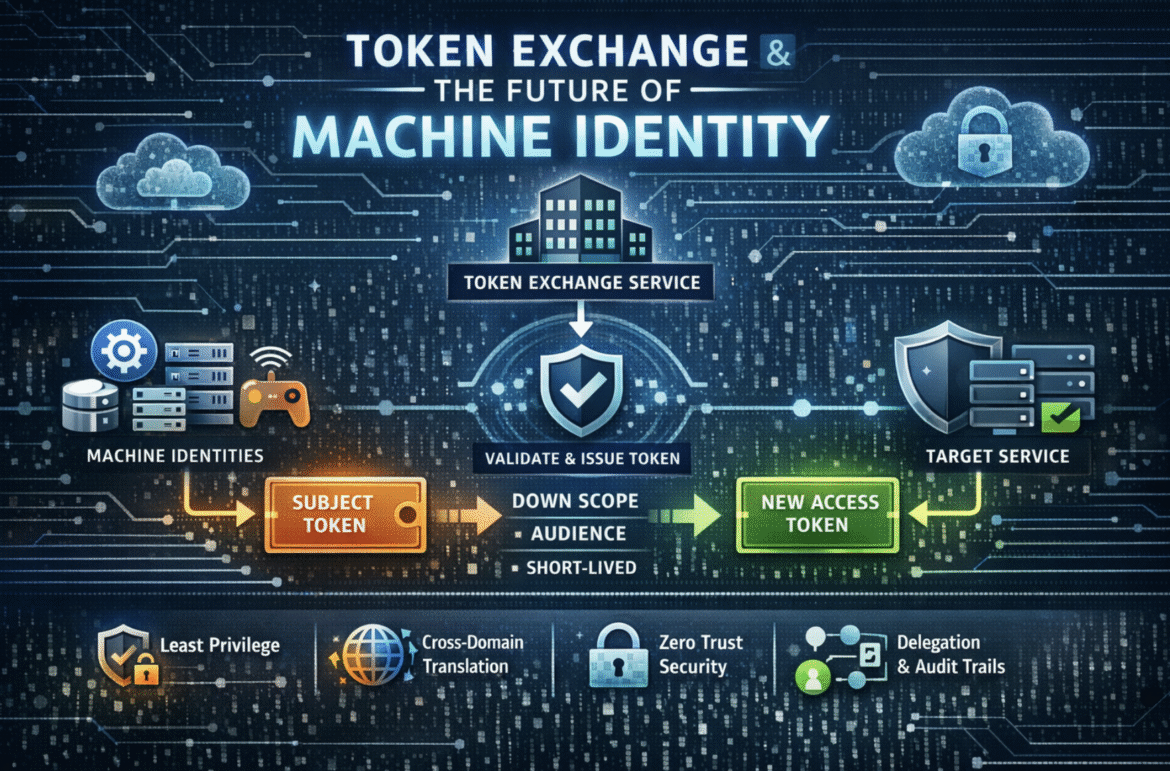
Token Exchange and the Future of Machine Identity
Machine identity is quietly becoming the dominant identity problem on the internet. Not user logins. Not passwords. Not MFA. It’s services, workloads, agents, pipelines, and devices authenticating to other services, at cloud scale, across networks you don’t fully control, with lifetimes measured in seconds. In that world, token exchange is more than an OAuth feature.…
-
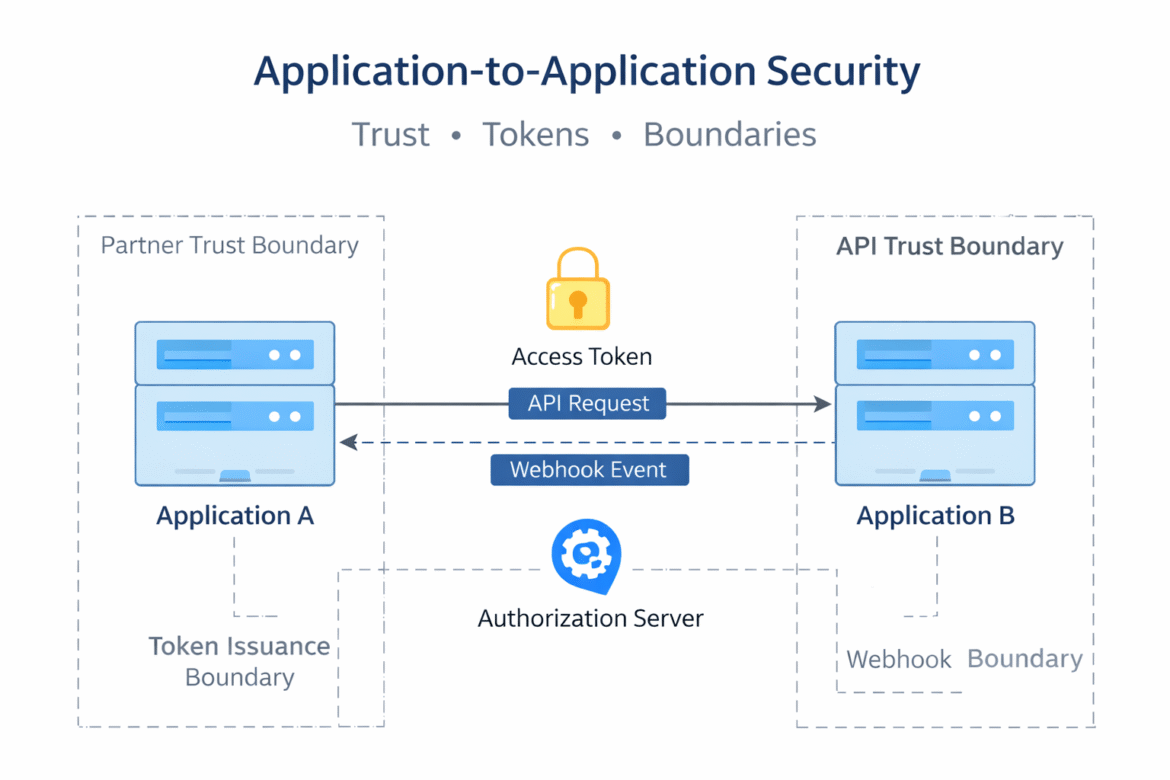
A2A Security Explained: Common Risks in Service-to-Service Integrations
Modern systems are no longer isolated applications. They are networks of services, partners, and platforms exchanging data and triggering actions across organizational boundaries. Application-to-Application (A2A) communication has become the backbone of SaaS ecosystems, internal microservices, and B2B integrations. Despite its importance, A2A security is often underestimated. Many teams assume that once authentication is in place,…
