Containers are often described as “isolated environments.” And for the most part, they are. But that isolation is not absolute.
At the core, containers share the same host kernel. And when that boundary is weakened, through misconfiguration or vulnerability, container escape becomes possible.
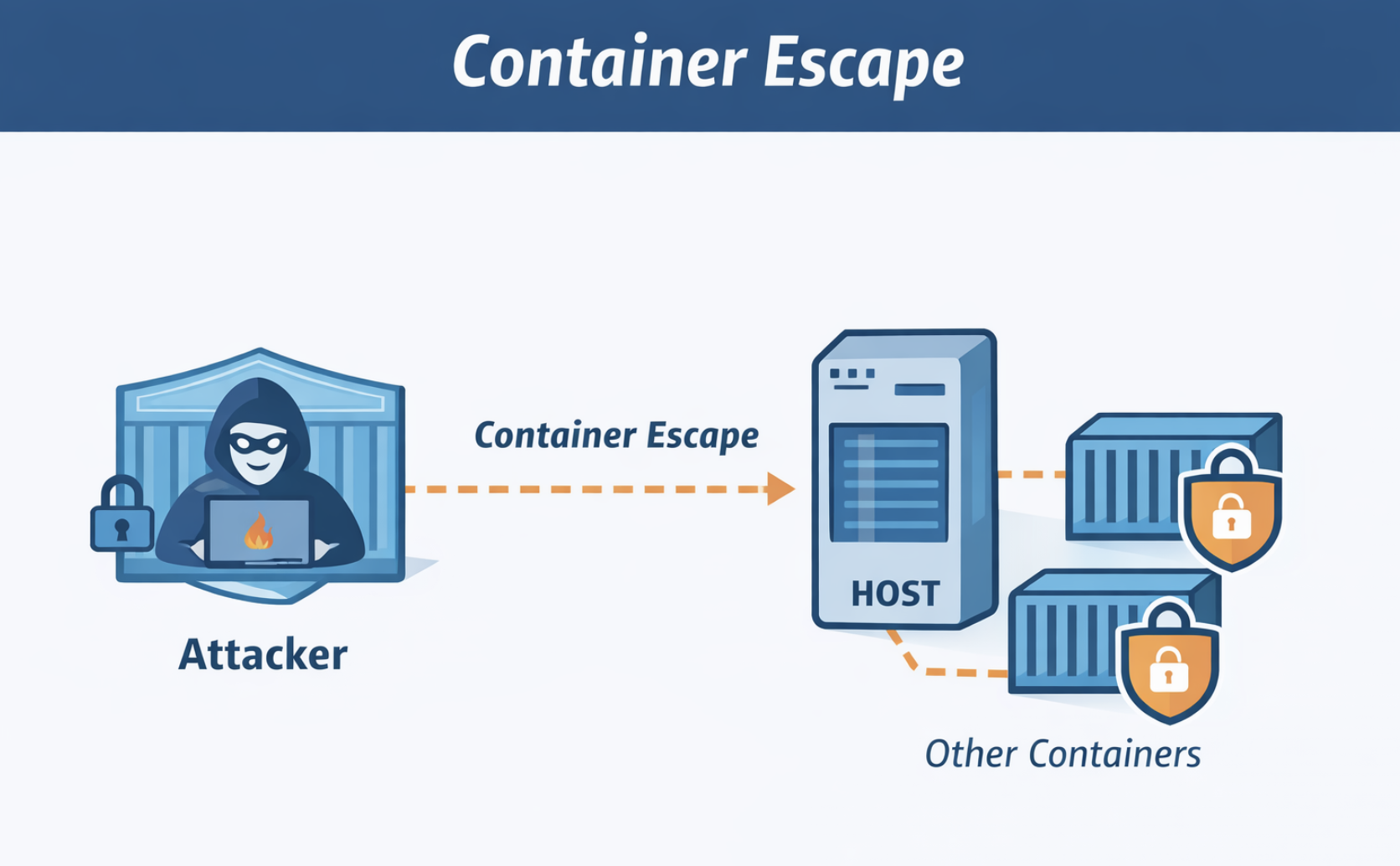
What is a Container Escape?
A container escape occurs when an attacker breaks out of a container and gains access to the host system or other containers.
Technically, containers rely on:
- Linux namespaces
- cgroups
- kernel-level isolation
If any of these layers are misconfigured or vulnerable, the boundary can be bypassed. Once that happens, the impact is severe:
- host compromise
- access to other workloads
- credential theft
- lateral movement across clusters
In modern environments, this can escalate from one compromised container to full infrastructure takeover.
Why Container Escape is a Growing Concern (2025-2026)
Recent vulnerabilities show that container escape is not theoretical it’s actively evolving.
- In 2025, multiple high-severity flaws in the container runtime (runC) allowed attackers to break isolation and gain host-level access
- These vulnerabilities affected nearly all major platforms, including Docker and Kubernetes
- Exploits demonstrated how attackers could manipulate mounts and system paths to write directly to critical host files
At the same time:
- New escape techniques (e.g., GPU toolkit exploits like “NVIDIAScape”) show how even specialized components can become attack paths
This reinforces a key reality: Containers are an isolation mechanism, not a security boundary.
How Container Escape Actually Happens
Let’s simplify the mechanics.
1. Exploiting the Shared Kernel
Containers do not have their own kernel.
If an attacker exploits:
- kernel vulnerabilities
- system calls
- filesystem interfaces
They can interact directly with the host.
2. Abusing Misconfigurations
Most real-world escapes don’t start with zero-days.
They start with:
- privileged containers
- root user inside container
- mounted host paths (
/var/run/docker.sock) - excessive Linux capabilities
These create direct paths to the host.
3. Runtime Vulnerabilities (Real Example)
In recent runC vulnerabilities:
- Attackers manipulated
/dev/nullmasking logic - Replaced it with a malicious symlink
- Forced the runtime to mount sensitive host paths
Result:
→ write access to /proc
→ privilege escalation
→ container escape
4. Mount & Filesystem Attacks
Attackers exploit:
- bind mounts
- shared volumes
- race conditions
Example:
- redirecting mount operations
- accessing protected host files before restrictions apply
What Happens After Escape?
Once outside the container:
- Full host access becomes possible
- Other containers can be targeted
- Kubernetes nodes can be compromised
- CI/CD pipelines can be poisoned
In clustered environments, this becomes a horizontal expansion problem. One weak container, entire cluster exposure.
How to Prevent Container Escape (Practical Approach)
Prevention is not about one control. t’s about layered reduction of risk.
1. Never Run as Root
USER appuser
Why:
- Limits privilege escalation
- Reduces impact even if escape occurs
2. Use Rootless Containers / User Namespaces
Map container root, non-root on host. This ensures even if attacker escapes, no real root access. Recommended in response to recent vulnerabilities
3. Drop Linux Capabilities
Default containers have more privileges than needed.
Run with:
--cap-drop=ALL
Add only what’s required.
4. Avoid Privileged Containers
Never use:
--privileged
This effectively removes isolation.
5. Use Read-Only Filesystems
readOnlyRootFilesystem: true
Prevents:
- payload persistence
- system tampering
6. Restrict Host Access
Avoid:
- mounting Docker socket
- mounting
/proc,/sys,/ - host network / PID namespace
These are direct escape enablers.
7. Apply Seccomp and AppArmor
These restrict system calls. Even if exploited, attacker capabilities are limited
8. Keep Runtime Updated
Many escape vulnerabilities are:
- runtime-level (runC, containerd)
- kernel-level
Regular patching is critical.
9. Use Stronger Isolation (When Needed)
For high-risk workloads:
- gVisor
- Kata Containers
These add an extra isolation boundary beyond the kernel.
10. Harden Kubernetes Pods
Use:
securityContext:
runAsNonRoot: true
allowPrivilegeEscalation: false
readOnlyRootFilesystem: true
capabilities:
drop: ["ALL"]
Also:
- enforce Pod Security Standards
- apply network policies
The Real Insight
Container escape is not just a vulnerability problem. It’s a design problem. Most successful escapes happen because:
- containers are over-privileged
- defaults are not hardened
- trust boundaries are unclear
Final Thought
Containers give the illusion of isolation. But in reality: You are always one misconfiguration away from the host.
Security doesn’t come from assuming isolation. It comes from actively reducing what a container is allowed to do.
Because the safest container is not the one that is hardest to break, It’s the one that has nothing useful to gain, even if broken.
Leave a Reply