Modern applications rarely run as a single system anymore. A single user request may travel through:
- API Gateways
- Authentication services
- Payment services
- Recommendation engines
- Kafka consumers
- Internal APIs
- AI inference pipelines
- Kubernetes workloads across multiple clusters
This architecture increases scalability and engineering velocity.
It also creates a dangerous security problem: How do services know they are talking to legitimate internal services and not an attacker sitting inside the network?
This is where mTLS (Mutual TLS) becomes critical.
mTLS is one of the foundational building blocks behind:
- Zero Trust architectures
- Service Mesh security
- Kubernetes east-west traffic protection
- Identity-aware microservices
- Secure service-to-service communication
And yet, many engineers still think mTLS is simply: “HTTPS, but both sides have certificates.”
That’s technically true. But architecturally incomplete. The real purpose of mTLS is not just encryption. It is:
- workload identity
- cryptographic trust
- authenticated service communication
- policy enforcement at runtime
This article explains how mTLS actually works between microservices: step-by-step with real architecture examples and production tradeoffs.
The Core Problem in Microservices
Imagine this architecture:
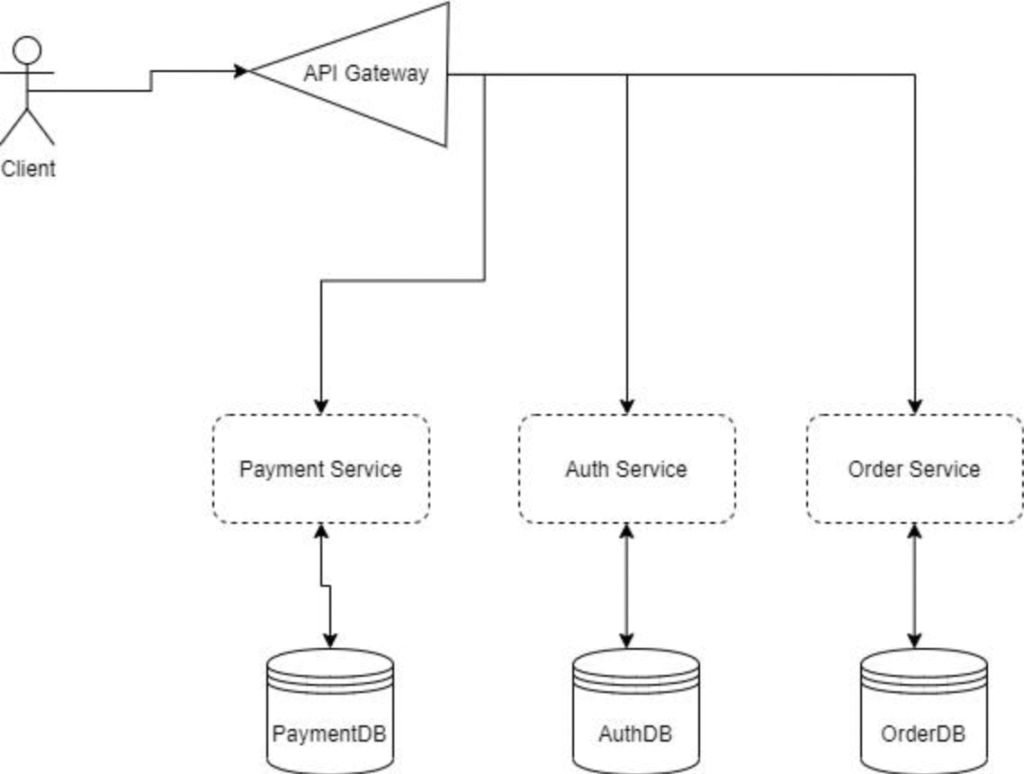
A request flows like this:
User → API Gateway → Auth Service → Payment Service → DatabaseWithout mTLS, internal services often trust:
- internal IP ranges
- VPC boundaries
- Kubernetes networking
- DNS names
- bearer tokens alone
This becomes dangerous because modern attacks often happen inside trusted infrastructure.
Examples:
- compromised pod in Kubernetes
- lateral movement after container escape
- SSRF into internal APIs
- rogue workloads
- poisoned CI/CD deployments
- stolen service account tokens
If an attacker gains access to one workload, they may impersonate internal services unless strong workload identity exists.
mTLS solves this by making every service prove its identity cryptographically.
What is mTLS?
Traditional HTTPS:
- server proves identity to client
- client usually remains anonymous
mTLS:
- server authenticates client
- client authenticates server
- both sides verify certificates
- communication becomes encrypted and identity-aware
In simple terms:
Service A says: “Prove you are Payment Service.”
Service B responds: “Here is my signed certificate issued by our trusted CA.”
Now both services trust each other cryptographically.
Step-by-Step mTLS Handshake
Let’s walk through an actual service-to-service flow.
Architecture: Frontend Service → Payment Service
Both services have:
- private keys
- certificates
- trusted Certificate Authority (CA)
Step 1: Connection Starts
Frontend Service initiates TLS connection: Frontend → Payment Service
Step 2: Payment Service Sends Certificate
Payment Service sends:
- public certificate
- certificate chain
Frontend verifies:
- trusted CA signed it
- certificate not expired
- service identity matches expectations
If verification fails: connection terminates immediately
Step 3: Frontend Sends Its Own Certificate
Now mutual authentication begins.
Frontend sends:
- its own certificate
- proof it owns the private key
Payment Service validates:
- trusted CA
- allowed workload identity
- certificate validity
Step 4: Secure Session Established
Only after both sides verify identity:
- symmetric session keys generated
- encrypted communication begins
Now traffic is:
- encrypted
- authenticated
- integrity-protected
What Actually Gets Verified?
mTLS is not merely checking: “Is this encrypted?”
It verifies:
- Who issued the certificate?
- Which workload owns it?
- Is it revoked?
- Is it expired?
- Does policy allow this workload to talk to this service?
This creates identity-aware networking.
Example: Kubernetes Without mTLS
Without mTLS: Pod A → Pod B
If network access exists, communication succeeds. This means:
- compromised workloads can impersonate services
- east-west traffic becomes risky
- lateral movement becomes easier
Kubernetes With mTLS
With mTLS: Pod A → Pod B
Pod B verifies:
- certificate issuer
- workload identity
- namespace policies
- service identity
Unauthorized workloads fail authentication immediately. This is one reason service meshes became popular.
Where Service Meshes Fit In
Technologies like:
- Istio
- Linkerd
- Consul
automate:
- certificate issuance
- certificate rotation
- policy enforcement
- workload identity
- encrypted east-west traffic
Instead of developers manually handling TLS everywhere, sidecars manage it automatically.
Example: Service A → Envoy Proxy → Envoy Proxy → Service B
The proxies establish mTLS transparently.
The Hidden Operational Problem: Certificate Management
mTLS sounds simple architecturally. Operationally, it becomes difficult at scale. Large environments may contain:
- thousands of workloads
- short-lived containers
- dynamic scaling
- multi-cluster deployments
Now you must manage:
- certificate issuance
- certificate rotation
- revocation
- trust distribution
- CA hierarchy
- workload identity lifecycle
This is why platforms use:
- SPIFFE
- SPIRE
- cert-manager
- Vault PKI
- cloud-managed identities
SPIFFE Changes Everything
SPIFFE introduces workload identity standards.
Instead of certificates identifying: server.company.internal
they identify workloads directly: spiffe://company/payment-service
This is extremely powerful for Zero Trust architectures. Identity becomes attached to workloads, not infrastructure.
Real-World Production Tradeoffs
mTLS improves security significantly. But it introduces complexity.
Advantages
- strong workload identity
- encrypted east-west traffic
- prevents impersonation
- reduces lateral movement
- enables Zero Trust architectures
- policy-based service communication
Challenges
- certificate lifecycle complexity
- operational overhead
- debugging difficulty
- latency overhead (usually small)
- service mesh complexity
- trust management across clusters
Many organizations fail not because mTLS is insecure but because certificate management becomes operationally fragile.
Common Misconfigurations
1. Long-Lived Certificates
Attackers love certificates valid for months or years. Modern systems rotate certificates aggressively.
2. Shared Certificates
Every workload should have unique identity. Shared certs destroy auditability.
3. Weak Internal Trust Assumptions
Many teams secure north-south traffic: Internet → Application
But ignore east-west traffic: Service → Service
Modern breaches increasingly exploit this gap.
4. “Allow All” Service Mesh Policies
Some deployments enable mTLS encryption but still allow unrestricted communication. Encryption alone is not Zero Trust. Identity-based authorization matters.
Where mTLS Matters Most
mTLS becomes especially important in:
- Kubernetes
- multi-tenant systems
- internal APIs
- fintech systems
- healthcare platforms
- AI inference systems
- multi-cluster environments
- zero trust architectures
- regulated workloads
Especially where:
- east-west traffic is high
- workloads scale dynamically
- identities change frequently
Final Thought
The biggest misconception about mTLS is thinking it is: “just encrypted traffic.”
It is not.
mTLS transforms the network from: IP-based trust ->to-> identity-based trust
That shift fundamentally changes how distributed systems defend against modern attacks.
In modern architectures:
- workloads are ephemeral
- infrastructure changes constantly
- attackers move laterally fast
The network itself can no longer be trusted. Identity becomes the new security boundary. And mTLS is one of the technologies making that possible.
Leave a Reply