Most systems are not insecure because developers don’t patch vulnerabilities.
They are insecure because they were never designed to be secure in the first place. We’ve normalized a cycle:
- Build fast
- Ship to production
- Scan for vulnerabilities
- Patch what’s found
And repeat. This feels like security. But it’s not. It’s damage control.
What is “Secure by Patch”?
Secure-by-patch is what most teams practice today.
It means:
- Fixing vulnerabilities after they are discovered
- Responding to CVEs, scans, and bug reports
- Treating security as a post-development activity
Examples:
- Fixing XSS after a penetration test
- Updating a vulnerable library after a CVE
- Patching container images weekly
The problem isn’t that patching is wrong. The problem is: patching alone can never make a system secure
What is “Secure by Design”?
Secure-by-design flips the model.
Instead of asking: “How do we fix vulnerabilities?”
It asks: “How do we design the system so vulnerabilities don’t become breaches?”
It includes:
- Defining trust boundaries
- Designing identity-first communication
- Enforcing least privilege by default
- Thinking in attack paths, not components
Security becomes an architectural property, not a checklist.
Secure-by-Patch vs Secure-by-Design
| Aspect | Secure-by-Patch | Secure-by-Design |
|---|---|---|
| Timing | After release | Before and during design |
| Approach | Reactive | Proactive |
| Focus | Individual vulnerabilities | System-level risk |
| Risk | Continuous exposure | Reduced attack surface |
| Example | Fixing auth bugs | Designing proper identity model |
Example: Microservices Architecture
Let’s make this concrete.
Secure-by-Patch Approach
- Services communicate over open internal network
- Authentication is inconsistent or missing
- Secrets are hardcoded or loosely managed
- Security issues are found later via scans
Result:
- Attackers move laterally
- One compromised service = full system compromise
Secure-by-Design Approach
- Every service has a strong identity
- Communication uses mTLS (mutual TLS)
- Access is enforced via least privilege policies
- Trust boundaries are clearly defined
Result:
- Even if one service is compromised, blast radius is limited
Sample Architecture Diagram
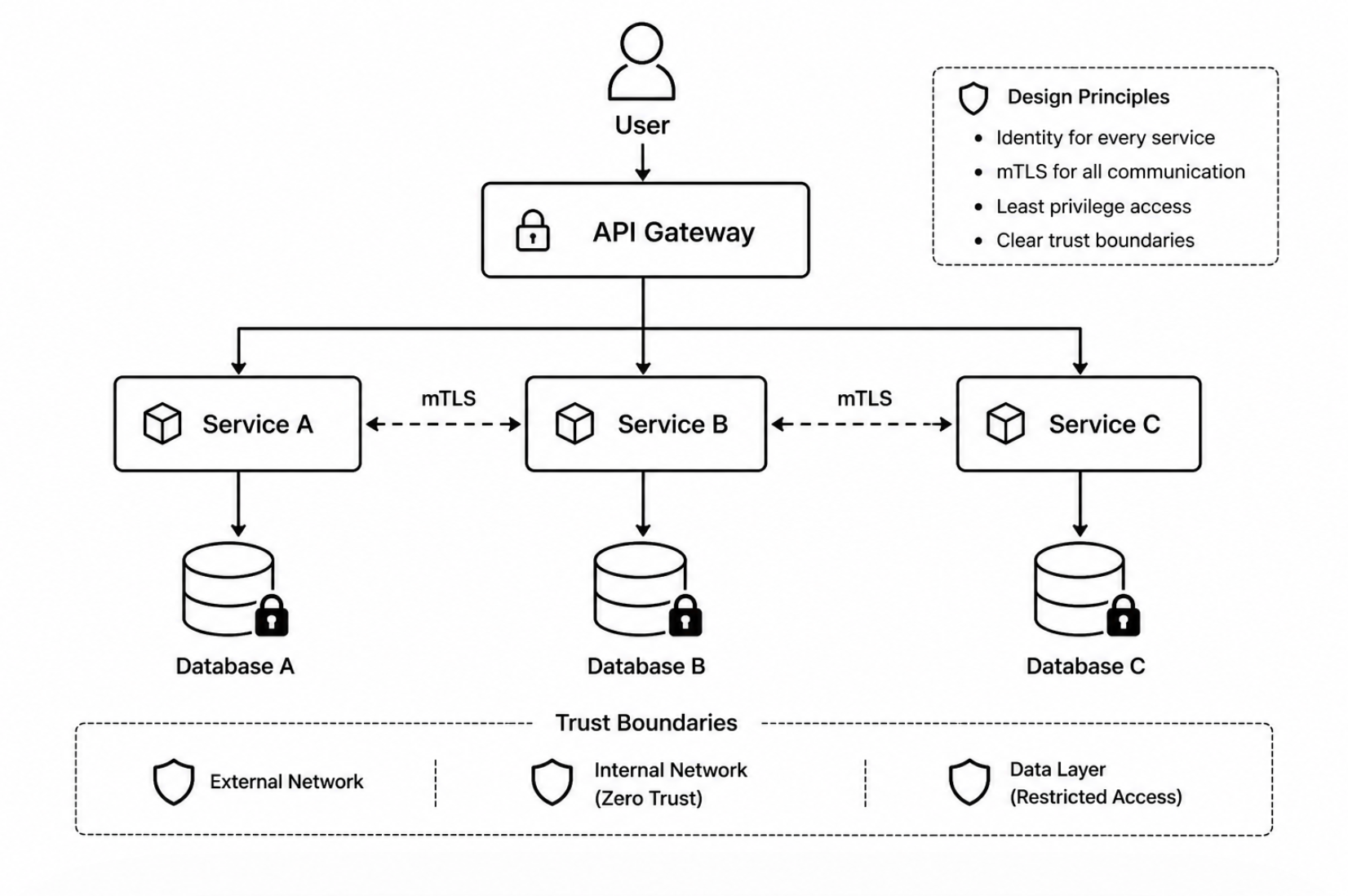
Secure-by-design architecture: identity-first communication with mTLS and least privilege
Key Design Elements:
– Every service has a unique identity
– mTLS enforces encrypted + authenticated communication
– Access between services is restricted (least privilege)
– No implicit trust inside the network
This is secure by design. Not dependent on patching to survive
Why Patching Alone Fails
Even with the best tools:
1. Unknown vulnerabilities always exist
You can’t patch what you don’t know.
2. Misconfigurations are not “patchable”
- Open S3 buckets
- Over-permissive IAM roles
- Exposed internal services
These are design failures, not bugs
3. Complex systems increase attack surface
Modern systems:
- Microservices
- APIs
- Third-party integrations
More components = more paths to exploit
4. Human error is constant
- Incorrect fixes
- Missed vulnerabilities
- Delayed patches
You cannot rely on perfection
How to Implement Secure-by-Design
This is where most content stays vague. Let’s make it practical.
1. Define Trust Boundaries Early
- What is internal vs external?
- What should never be directly exposed?
2. Use Identity-First Architecture
- Every service must authenticate
- No anonymous internal communication
3. Apply Least Privilege Everywhere
- Services access only what they need
- No broad permissions
4. Threat Model Before Building
- Identify attack paths
- Think like an attacker
5. Secure Defaults
- Deny by default
- Explicit allow only
The Real Shift
Secure-by-patch asks: “What vulnerabilities do we have?”
Secure-by-design asks: “What attacks are even possible?”
That shift changes everything.
Final Thought
You cannot patch your way to security. You can only design your way there.
If you’re building cloud or AI systems
Security is no longer about tools. It’s about how your system is structured.
Explore more deep dives on system-level security on this site.
Leave a Reply