Modern distributed systems rely heavily on APIs and service-to-service communication. Whether it is a mobile app calling a backend, a partner integrating through APIs, or microservices communicating inside a Kubernetes cluster, establishing trust between systems is fundamental to security architecture.
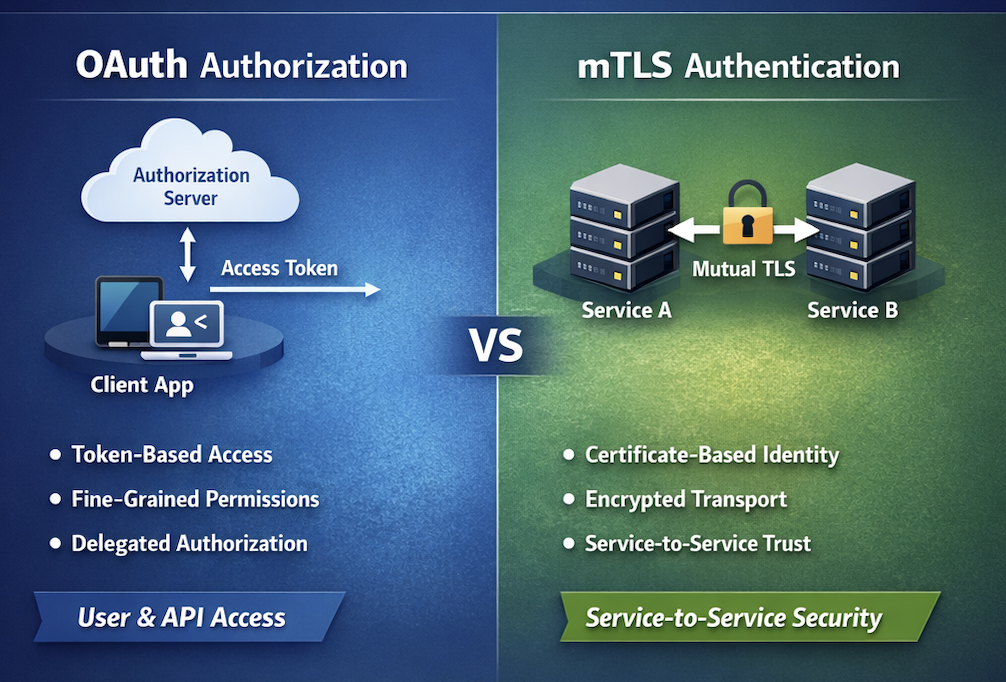
Two commonly used trust mechanisms are OAuth (token-based authorization) and mTLS (mutual TLS authentication). While both provide mechanisms for securing communication, they solve different security problems and operate at different layers of the system architecture.
Understanding when to use OAuth, when to use mTLS, and when to combine them is critical for designing secure modern systems.
Understanding the Trust Model Problem
Before comparing OAuth and mTLS, it is important to understand what trust problem we are solving. When two systems communicate, three fundamental questions arise:
- Who are you? (Authentication)
- What are you allowed to do? (Authorization)
- Can I trust the connection between us? (Secure channel)
Different mechanisms solve different parts of this puzzle.
| Security Problem | Typical Solution |
|---|---|
| Authentication | mTLS, certificates, identity providers |
| Authorization | OAuth tokens, access policies |
| Transport security | TLS |
OAuth and mTLS are often mistakenly treated as interchangeable, but they actually address different layers of trust.
What is mTLS (Mutual TLS)?
Mutual TLS extends standard TLS by requiring both the client and the server to authenticate using certificates.
In traditional TLS:
- The server proves its identity using a certificate.
- The client verifies the server.
- The client usually remains anonymous.
With mutual TLS, both parties authenticate each other using certificates issued by a trusted Certificate Authority (CA).
mTLS Authentication Flow
- Client initiates TLS handshake.
- Server presents its certificate.
- Client verifies server certificate.
- Server requests client certificate.
- Client sends certificate.
- Server verifies client certificate against trusted CA.
- Secure encrypted channel is established.
The result: Both parties cryptographically verify each other’s identity before communication begins.
Advantages of mTLS
Strong Identity Assurance
Certificates provide cryptographic proof of identity. This is particularly useful in machine-to-machine communication.
Example: Microservice A proves its identity to Microservice B using a certificate.
Network-Level Security
mTLS operates at the transport layer, meaning security is enforced before application logic executes.
This reduces risk from:
- API abuse
- Unauthorized service calls
- Man-in-the-middle attacks
Ideal for Internal Service Communication
mTLS is widely used in:
- Service meshes (Istio, Linkerd)
- Zero Trust architectures
- Internal microservice communication
Example:
Service A -> Service B
Identity verified via certificate
Traffic encrypted via TLS
Limitations of mTLS
Despite its strengths, mTLS has operational challenges.
Certificate Management Complexity
Large environments require managing:
- Certificate issuance
- Certificate rotation
- Certificate revocation
- CA trust chains
This becomes difficult at scale.
Lack of Granular Authorization
mTLS answers “who are you?”, but not “what are you allowed to do?”.
Example: A service may authenticate successfully but still require fine-grained access control.
What is OAuth?
OAuth is an authorization framework designed to allow applications to access resources on behalf of a user or service.
Instead of relying on certificates, OAuth uses tokens issued by an authorization server. The most common version used today is OAuth 2.0 with JWT tokens.
OAuth Authorization Flow
Typical OAuth flow:
- Client requests authorization.
- Authorization server authenticates client/user.
- Authorization server issues an access token.
- Client sends token to resource server.
- Resource server validates token.
- Access is granted based on token scope.
Example OAuth Token
A typical JWT token may contain:
{
"iss": "auth.company.com",
"sub": "service-A",
"aud": "payments-api",
"scope": "payments:write",
"exp": 1712458821
}
This token allows fine-grained authorization decisions.
Advantages of OAuth
Fine-Grained Authorization
OAuth allows defining scopes and permissions.
Example:
| Token Scope | Allowed Action |
|---|---|
| payments:read | Read payment data |
| payments:write | Create transactions |
| admin:manage | Administrative operations |
Delegated Authorization
OAuth enables third-party access without sharing credentials.
Example:
User -> Google -> Third Party App
The user grants access via OAuth.
API Ecosystem Standard
OAuth is widely used for:
- Public APIs
- Mobile apps
- Partner integrations
- SaaS platforms
Examples:
- Google APIs
- GitHub APIs
- Stripe APIs
Token-Based Architecture
OAuth works well with:
- API gateways
- Serverless platforms
- Edge authentication
Tokens can be validated quickly without database lookups.
Limitations of OAuth
Despite its flexibility, OAuth does not inherently verify client identity at the transport layer.
Token Theft Risk
If tokens are leaked:
- Attackers can replay requests
- Unauthorized access becomes possible
Mitigations include:
- Token binding
- Short token lifetimes
- Proof-of-possession tokens
Dependency on Identity Infrastructure
OAuth requires:
- Authorization server
- Token validation logic
- Key rotation infrastructure
This introduces additional operational complexity.
OAuth vs mTLS: Architectural Differences
| Aspect | OAuth | mTLS |
|---|---|---|
| Layer | Application | Transport |
| Purpose | Authorization | Authentication |
| Identity | Token-based | Certificate-based |
| Granularity | Fine-grained scopes | Binary trust |
| Operational Complexity | Identity infrastructure | Certificate management |
| Best For | APIs and user delegation | Service-to-service trust |
When to Use mTLS
mTLS is ideal when:
1. Service-to-Service Communication
Example:
Microservice A -> Microservice B
In internal infrastructure.
2. Zero Trust Architectures
Zero trust requires strong identity verification for every request.
mTLS ensures:
- Verified service identity
- Encrypted communication
3. High-Security Environments
Examples:
- Financial systems
- Healthcare platforms
- Government systems
When to Use OAuth
OAuth is best suited for:
1. API Authorization
Example:
Mobile App -> Backend API
Where the backend needs to understand user permissions.
2. Partner Integrations
Example:
Partner System -> Company API
OAuth allows controlled delegated access.
3. SaaS Platforms
SaaS ecosystems rely on OAuth for:
- Multi-tenant access
- Third-party integrations
- User-based permissions
Combining OAuth and mTLS
In many modern architectures, the most secure approach is combining both mechanisms.
Example architecture:
Client ----mTLS----> API Gateway ----OAuth----> Microservice
or
Service A --mTLS--> Service Mesh
Service Mesh validates identity
OAuth token validates authorization
Here:
- mTLS ensures identity and encrypted transport
- OAuth ensures authorization and access control
This layered model aligns with defense-in-depth security principles.
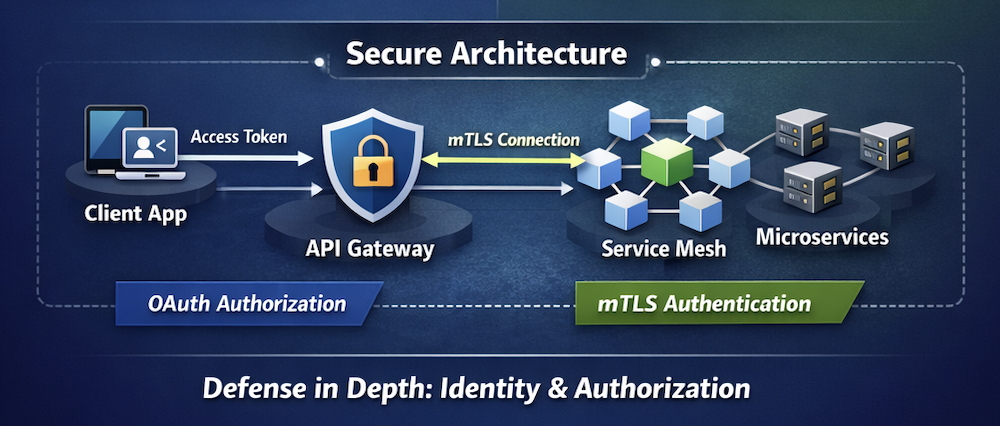
Real-World Example Architecture
Example secure API architecture:
Client App
│
│ OAuth Token
▼
API Gateway
│
│ mTLS
▼
Service Mesh
│
│ OAuth validation
▼
Microservices
Security benefits:
- Strong identity verification
- Encrypted communication
- Fine-grained authorization
Security Pitfalls to Avoid
Treating OAuth as Authentication
OAuth primarily handles authorization, not authentication.
Use OIDC (OpenID Connect) when identity verification is required.
Ignoring Certificate Lifecycle
mTLS deployments fail when:
- Certificates expire
- Rotation processes break
Automation is essential.
Over-Trusting Internal Networks
Many breaches occur due to implicit trust within internal networks.
mTLS eliminates this assumption.
Final Thoughts
OAuth and mTLS are not competing technologies, they solve different trust problems.
mTLS provides strong identity verification and encrypted communication, making it ideal for service-to-service trust.
OAuth provides fine-grained authorization and delegated access, making it essential for modern API ecosystems.
The most resilient architectures often combine both, creating layered trust models aligned with Zero Trust principles.
As systems grow more distributed with microservices, service meshes, and third-party integrations, the ability to design the right trust model becomes a core security architecture skill.


Leave a Reply